What are DLTs and blockchains?
-
Due to the Data (Use and Access) Act coming into law on 19 June 2025, this guidance is under review and may be subject to change. The Plans for new and updated guidance page will tell you about which guidance will be updated and when this will happen.
In detail
- What is a distributed ledger technology (DLT)?
- What is a blockchain?
- How do blockchains work?
- What is ‘on’ the blockchain?
- What are the different types of blockchain?
What is distributed ledger technology (DLT)?
A distributed ledger technology (DLT) is a type of digital system that allows simultaneous access, validation, and record-keeping across a distributed database maintained by multiple users.
Ledgers are a long-established and trusted way to record financial transactions. Traditionally, ledgers were physical record-keeping books. Over time, they evolved to electronic ledgers on spreadsheets and then databases. Typically, recordkeeping has been a centralised process that requires trust in the bookkeeper or organisation maintaining it.
DLT allows an electronic ledger to be created, shared, added to and synchronised in real time. It allows multiple parties to maintain records simultaneously instead of always being under the overall control of a single party.
A DLT is different from a traditional ledger because:
- there is no single record keeper; and
- the parties transacting via the ledger do not need to know or trust each other.
Instead, the inherent properties of a DLT ensure that the ledger remains accurate and up to date. These properties are below:
- Decentralisation: This means that there is no identified single authority who checks the accuracy of transaction records. Instead, the parties maintain the ledger through a collaborative record-keeping process.
- Transparency: Once a transaction is added to the ledger, everyone in the network can see it. Everyone always has the same version of the ledger.
- Immutability: No one can alter or remove the ledger’s content. For this reason, DLTs are sometimes known as ‘append only’ databases because they cannot be edited, only added to.
What is a blockchain?
There are different types of DLT depending on how they structure the data they record. One of the most well-known DLTs is blockchain.
Blockchain records transactions in a linear fashion in blocks of data that are linked by a cryptographic reference, forming a growing list of records. This link between consecutive data blocks prevents the alteration of any data in a block once added to the ledger (at least not without changing later blocks and potentially ‘forking’ the blockchain, ie splitting the ledger into two separate blockchains). The immutable nature of blockchain is due to this link between two consecutive blocks.
Blockchain is the most common type of DLT currently in use. Well-known examples include Bitcoin and Ethereum blockchain platforms. For this reason, this guidance uses the terms ‘blockchain’ and ‘DLT’ interchangeably. However, the guidance also applies to other types of DLTs that structure data in different ways, such as DLTs like Hedera or IOTA.
How do blockchains work?
In a blockchain, all members maintain the ledger using a collaborative process known as consensus mechanism. The transactions are recorded in blocks. These blocks are arranged one after the other, linked via a cryptographic reference, creating a chain.
To ensure the integrity of the ledger, each new block is linked to the previous one via a cryptographic hash. The link is made by applying a cryptographic hash function to the contents of the previous block and storing the resulting hash within the next block, as shown in Figure 1.
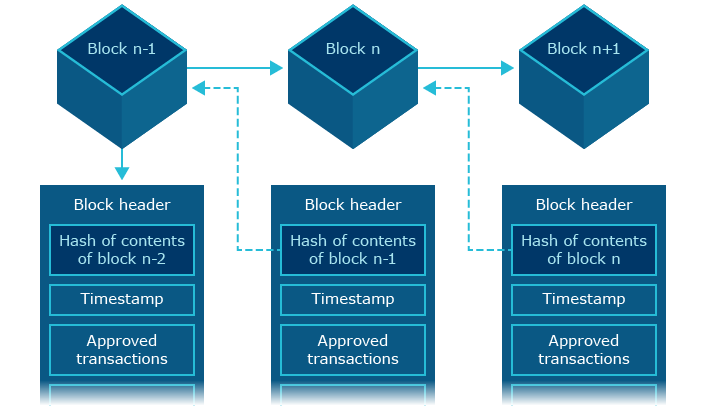
Figure 1: Blocks in a blockchain
The consistent link between the blocks provides a level of assurance that no single participant can change records once they are added to the ledger. In turn, this means that all parties can trust that the ledger is a complete and accurate record.
How are transactions validated in a blockchain?
In order to understand how blockchains work, it’s essential to understand how transactions are validated.
When a new transaction is created, it is transmitted in the blockchain network. The new transaction is added to a pool of pending transactions awaiting approval. Depending on the consensus mechanism, the validator nodes will bundle a selection of these transactions to create a block. The validator nodes then use the consensus mechanism to validate the newly-created block. The consensus mechanism is a set of protocols that lays down the rules which the validators use to verify the transactions.
There are several types of consensus mechanism, such as Proof-of-Work (‘PoW’), Proof-of-Stake (‘PoS’) and Byzantine. Once all the transactions in that block are validated, the block is confirmed and added to the end of the blockchain, becoming a permanent entry into the immutable record. As more blocks are added to the chain, approved blocks get further confirmation, reinforcing their position in the chain. In certain consensus mechanisms, the validator nodes are incentivised for validating the transactions and maintaining the blockchain’s security.
What are the different types of roles in a blockchain?
The three main types of roles (nodes) observed in a blockchain are as follows:
- Accessors (read-only access): nodes that can join the blockchain and read the transaction.
- Participants: nodes that have the right to join the blockchain and send transactions for validation to the network. Participants have the right to interact with smart contracts installed on the blockchain (ie self-executing programs that automatically run when certain conditions are met).
- Validators: nodes permitted to validate transactions to create new blocks as defined by the consensus mechanism.
Nodes can have more than one role in a network. For example, a node can host a copy of the ledger, send transactions to the network and also participate in block validation. In this example, the node assumes all the roles outlined above. Alternatively, in some cases a node may only be permitted to join and read the transactions but not send or validate them. In this example, it has read-only access. Depending on the underlying blockchain protocol and node configuration, nodes can change roles after joining.
Apart from the node roles described above, there are other actors that are part of the ecosystem without joining the blockchain network itself. These include:
- developers who develop blockchain infrastructure;
- application developers;
- node operators on behalf of businesses;
- organisations acting as auditors; or
- governance participants.
What is ‘on’ the blockchain?
Information held on blockchain is known as ‘on-chain data’. On-chain data may be stored in various forms such as plaintext (unencrypted), hashed or encrypted. There are three main categories of on-chain data, which are:
- transactions;
- smart contracts; and
- metadata.
What are ‘transactions’?
Transactions account for the bulk of on-chain data. These are records of activities, such as:
- transfers of on-chain digital assets (such as Bitcoin) from one account to another;
- creation of smart contracts; and
- interactions with smart contracts, ie sending requests to the smart contract for processing.
The information contained in a transaction may include:
- the transaction identifier;
- sender and receiver wallet addresses;
- details on value of token or type of token transferred;
- Information or payload sent in smart contract transactions (eg if any functions were called up); and
- details of token creation (such as token identifier and type) in case a smart contract generates a token.
What are ‘smart contracts’?
A smart contract is a self-executing program stored on a blockchain that runs automatically when it meets predefined conditions. It can automate agreements and processes without the need for intermediaries. Importantly, smart contracts don’t use legal wording such as terms and conditions, like normal contracts do.
Information stored on smart contracts includes self-executing instructions (contract code) and data. The data stored in smart contracts can increase over time as the code interacts with incoming transactions. Every smart contract deployed on blockchain has a unique address to allow interaction with it.
What is ‘metadata’ in the blockchain context?
In blockchain, metadata is additional descriptive information about the block creation, ie ‘data about the data’. This can include:
- the block header;
- the time stamp of block creation;
- the Merkle-Root of a block; and
- event logs.
What are the types of transaction in a blockchain?
Depending on the blockchain, there are two broad types of transaction that a blockchain supports:
- regular transactions; and
- smart contract transactions.
Regular transactions are about transferring an asset from one account to another. For example, when one account holder sends a certain amount of Bitcoin to another account.
Blockchains that support smart contracts enable additional types of transactions. These blockchains can offer more functionality — such as the ability to build applications on blockchains.
Smart contracts can store data, such as code or logic for processing and real-world values (data points such as exchange rates or election results),on the underlying blockchain. Smart-contract data is therefore also a type of on-chain data.
Example
A company uses smart contracts on a blockchain platform to automate concert ticket sales.
It encodes all the information about ticket purchases in the smart contract, including terms of purchase logic to automate ticket prices for different scenarios. For example, varying the ticket prices based on the specific venue or seating zone. When a user starts buying a ticket on the platform, it triggers the smart contract, which validates the terms of purchase logic in code showing the prices based on that logic. The smart contract is programmed to recognise when the user has paid. Upon confirming the payment, the smart contract automatically transfers the ticket to the user’s account on the ticketing website. This complete process happens automatically without requiring a ticket agent or any intermediary.
The blockchain platform records the entire transaction.
What are the different types of blockchain?
In the context of this guidance, blockchains can be categorised based on factors such as:
- how open or restrictive the network is;
- its governance structure; and
- the type of consensus mechanism.
This guidance focuses on the common categorisation of blockchains as ‘permissionless’ or ‘permissioned’.
A permissionless blockchain is an open network which is accessible to anyone. Participants do not need to reveal their identities. Anyone can act as a user, validator or developer.
A permissioned blockchain is a closed network where only selected participants can join. The blockchain is typically controlled by a single entity or a consortium of entities (a ‘federated’ network). Usually, participants must establish their identity and only selected nodes in the network can act as validators. This also means that a permissioned blockchain may define the level of access for each participant.
Blockchains where data is publicly available are known as public blockchains. If the on-chain data is not publicly available, they are called private blockchains.
Different combinations of these types of blockchains are available:
- Public permissionless blockchains like Ethereum and Bitcoin.
Anyone can join these networks, run a blockchain node and assume any role. There is no restriction on visibility or accessibility of the information available on the chain. - Private permissioned blockchains are run on platforms like Enterprise Ethereum or Hyperledger Fabric. Those that are run by a group of entities are also known as consortium blockchains. They are closed networks that require an invitation to join. The consortium assign a node its role. There may be specific controls on the visibility and accessibility of data.
- Public permissioned blockchains like LACChain and EBSI. These combine the access restrictions of permissioned blockchains with the data visibility of permissionless ones. Just like private-permissioned blockchains, they can only be joined by invitation and nodes are assigned specific roles. However, anyone can access the data on the blockchain.
There is no such thing as a ‘private permissionless blockchain’. This is because the concepts of central control and no overall control are fundamentally opposed to each other.
A core principle of permissionless blockchains is their decentralised nature. They function without a central, single ‘owner’ that authorises transactions and maintains the records. However, blockchains as a whole can also be categorised on a spectrum based on the level of decentralisation they involve. For example, a traditional non-blockchain database solution is highly centralised while a public permissionless blockchain can be deemed highly decentralised. The private permissioned blockchain will be closer to the centralised end while a public permissioned blockchain gravitates towards the decentralised end. Figure 2 illustrates this spectrum. This consideration is crucial to understand the governance structure of a blockchain platform and identify the roles undertaken by blockchain users.
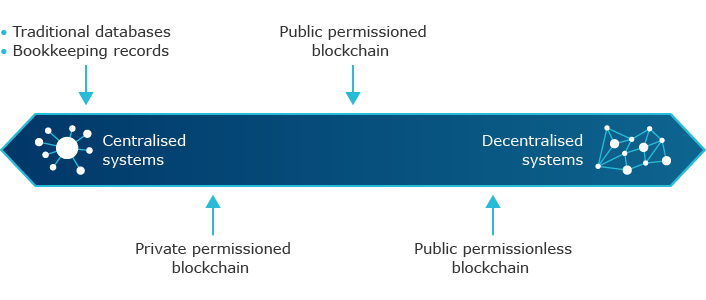
Figure 2 – Spectrum of blockchain decentralisation
What are the characteristics of a permissionless blockchain?
In a permissionless (public permissionless) blockchain, participants:
- can join or leave the network at any given time;
- do not need to go through any checking or vetting process;
- can view and observe transactions taking place on the network;
- can send their own transactions for validation and even participate in transaction validation (if they meet the specific technical requirements to do so); and
- are incentivised to perform the validation as defined in the consensus mechanism.
Permissionless blockchains operate under a decentralised governance model. This means participants make decisions by consensus about transaction validation and major network updates rather than by a single, central decision-maker.
Because the real-word identities of nodes on a permissionless blockchain are unknown, it cannot be assumed that nodes are trustworthy, or that they will always act in the platform’s best interests.
In this ‘trustless’ scenario, the trust is provided by the design of the network itself rather than the participants. This approach has many features in common with permissioned blockchains such as immutability and transparency. A key difference is the way that consensus is reached in order to maintain the integrity of the blockchain.
Consensus mechanisms in a permissionless blockchain are usually based on an incentive mechanism such as Proof of Work (PoW) where miners are rewarded for using computational power to propose and validate new blocks, and Proof of Stake (PoS) where validators or stakers are rewarded for participating in block validation and consensus based on the amount of cryptocurrency they stake).
In permissionless blockchains, consensus mechanisms tend to be complex and time-consuming. However, this is not always the case. Research and innovation have led to modern consensus mechanisms with improved speed and computational efficiency. For example, in 2022 the Ethereum blockchain platform changed their consensus mechanism from PoW to PoS for better energy efficiency, lower hardware entry requirements for validation and better scalability.
Public permissionless blockchains are often used in applications that involve cryptocurrency and other forms of digital assets. Collectively, these activities are called decentralised finance (DeFi). DeFi is an umbrella term, referring to financial instruments and services designed using DLT infrastructure. It does not have intermediaries for payment settlement like a traditional financial system and works on a peer-to-peer settlement model.
Public permissionless blockchain
An example of a public permissionless blockchain is the Bitcoin blockchain. Anyone can join this network, create an account and even start validating the transactions. Users can immediately start transacting to send or receive bitcoins.
Another popular public permissionless network is the Ethereum blockchain. Ethereum blockchain supports smart contract functionality and allows users to install smart contracts on it. Smart contracts enable the deployments of various types of applications on the Ethereum blockchain.
What are the characteristics of a permissioned blockchain?
In a permissioned blockchain, participants:
- are selected or invited by the blockchain administrator(s) to join the network;
- need to go through an identity verification process;
- must accept the terms and conditions;
- may have restricted access to view and observe certain information on the blockchain network;
- may have their roles restricted through rules defined by the administrator; and
- may not be incentivised for performing validation. Instead, certain nodes are pre-selected or hired to do so.
Permissioned blockchains are not completely trustless in the same way as permissionless blockchains. This is because only authorised users can join and access the network, according to the rules the administrator(s) determine. The identity of these users, and how far these users are ‘trusted’, is baked into the governance model of these blockchains. Users can determine the roles of nodes in a permissioned blockchain.
The development of digital public infrastructure has seen an uptake of public permissioned blockchains, where blockchain properties like transparency and public verifiability are crucial. For example, organisations using this technology for digital identity services, to digitise land registries or for educational qualification checks.
Example
The European Blockchain Services Infrastructure (EBSI) is an example of a public permissioned blockchain. Established by EU Member States along with Norway and Lichtenstein, it is designed to support trusted digital services (eg diplomas, identity, notary).
The consortium maintains the nodes while the blockchain built on them are open to anyone to perform verification on for a range of use-cases, like identity verification.
EBSI stores information in a trusted, decentralised way, allowing for new forms of ID verification for people and organisations within the EU and associated countries supporting EBSI.
Private permissioned blockchains are more appropriate for organisations for particular use cases, such as the supply-chain or private financial services that require properties like traceability, immutability and verifiability.
Example
A large car manufacturer pilots a blockchain solution to enable greater transparency of all transactions between participating partners in its supply chain.
The blockchain solution tracks the origin of all components throughout their lifecycle without the possibility of data manipulation.
The ability for all parties to have a real-time ‘single source of truth’ provides an ability to track components throughout the supply chain, without costly integration of IT systems across all participants.